Sometimes, after you use BitLocker to encrypt drives, you might also want to set a PIN for Windows 10 BitLocker to prevent BitLocker from Pre-boot attacks.
Contents:
- Enable a Pre-Boot BitLocker Pin Overview
- How to Enable Pre-Boot BitLocker PIN?
- How to Add a Pre-boot BitLocker PIN to Windows 10?
- How to Change BitLocker PIN Windows 10?
Enable a Pre-Boot BitLocker Pin Overview
To let BitLocker prompt for password at boot, you need a pre-boot password for this full-disk encryption. Though the system drive is encrypted by this encryption tool and you have also added a PIN for BitLocker Windows 10, it just pops up at startup with BitLocker a password instead of a PIN.
When Password VS PIN, most users would like to enable the Pre-boot BitLocker PIN on Windows 10 rather than a password. If you wish to boot with BitLocker Drive Encryption passwords, it is also available to disable Pre-boot authentication to make it possible of BitLocker not asking for PIN.
This article focuses on explaining to you how to allow enhanced PIN for startup with BitLocker, which is to say, telling you the way of enabling a Pre-boot BitLocker PIN on Windows 10.
How to Enable a Pre-Boot BitLocker PIN on Windows?
Before you get started to set up a pre-boot BitLocker PIN in Windows 10, make sure you have turned on BitLocker encryption. Or for some people who have no Trusted Platform Module chip on Windows 10, you can try to enable BitLocker without TPM.
Then you are capable of using group policy editor to enable BitLocker authentication in Windows 10.
1. Hit Windows +R to activate the Run box.
2. Type in gpedit.msc in the box and click OK to navigate to Group Policy.
3. In Local Group Policy, follow the path:
Computer Configuration / Administrative Templates / Windows Components / BitLocker Drive Encryption / Operating System Drives
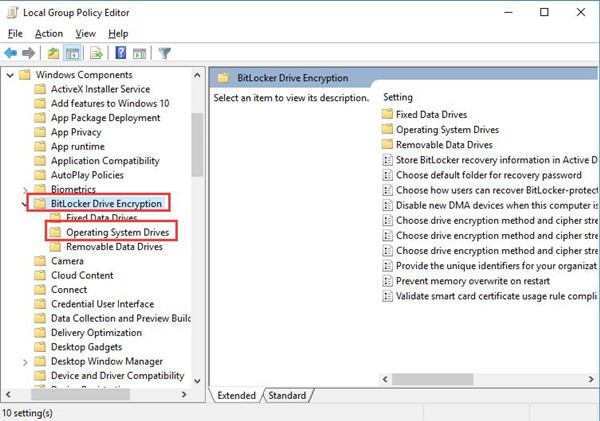
4. Under Operating System Drives, locate and right click Require additional authentication at startup to Edit it in the right sub-window.
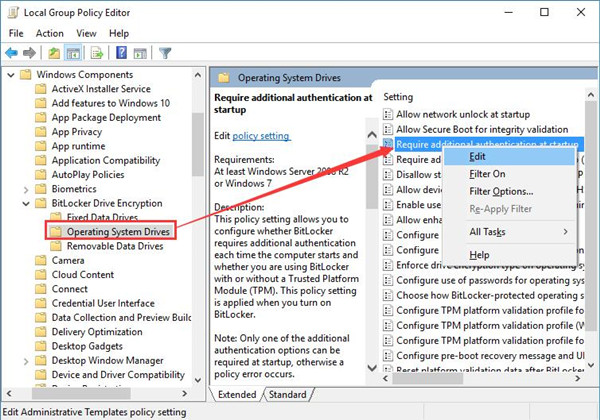
5. Set the option Require additional authentic at startup as Enabled, and then Choose to Configure TPM startup PIN and select Require startup PIN with TPM.
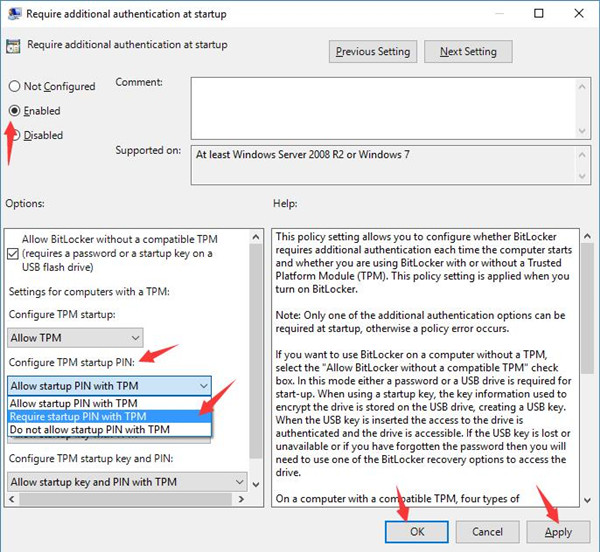
6. Finally, click Apply and OK to take effect.
At this time, you will have successfully enabled the Pre-boot BitLocker PIN for Windows 10. Maybe you feel like to add a PIN for BitLocker, go further.
How to Add a Pre-boot BitLocker PIN to Windows 10?
It is rather simple to make a PIN for BitLocker at startup on the occasion where you have chosen to make BitLocker prompt for password at boot.
1. Type in Command Prompt in the Start search box and then right click the best result to Run as administrator.
2. Copy manage-bde –protectors –add c: -TPMAndPIN in the command prompt and then press Enter to run it.
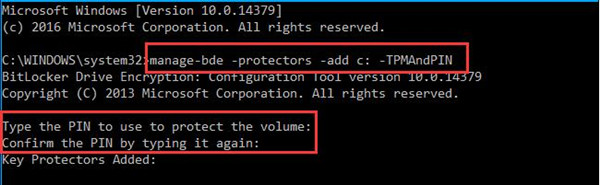
Here if your encrypted drive is not Local disk C:, you can change C: in this command to any other drives.
Then you will be prompted to enter a PIN for Windows 10 BitLocker and confirm it again.
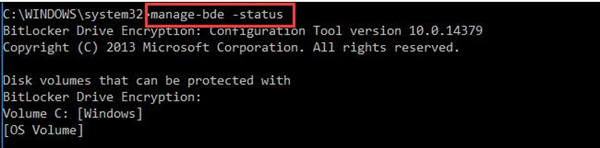
3. Check if the Key Protectors are added by entering the command: manage –bde -status
Once you have added the pre-boot BitLocker PIN on Windows 10, the next time you log on to your PC, you need BitLocker authentication with PIN.
How to Change BitLocker PIN Windows 10?
Sometimes, if you want to change the enhanced PIN in BitLocker, just complete the command manage-dbe Changepin -c: in Command prompt.
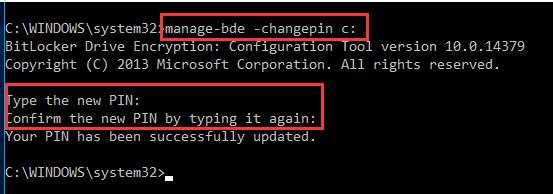
When you input the changed PIN in the command prompt and confirmed it, it means you are required to type in this new pre-boot PIN for BitLocker Drive Encryption to login in.
In a word, concentrating on enabling pre-boot PIN in BitLocker, this post also shows you how to add and change BitLocker Pin on Windows 10. If you want to disable a pre-boot BitLocker PIN after some time, just do the opposite.
More Articles:
What is Syskey and Why is it Not Supported Now on Windows 10